Operator-led, continuously delivered.
ThreatLayer is a managed cybersecurity program with expert execution, recurring validation, and accountable follow-through, supported by a unified platform.
ThreatLayer delivers operator-led security assessments, continuous visibility, and measurable risk reduction through a unified security program.
ThreatLayer runs as a managed security program, supported by a unified platform that preserves context, connects evidence, and proves progress over time.
Operators validate material risk. Strike Chain maps real paths to compromise. Remediation focuses on what breaks the most attack paths. Overwatch reports outcomes leadership can act on.
ThreatLayer combines expert-led execution, continuous assessment, and attack path intelligence into a single, accountable security program.
ThreatLayer supports leadership teams across finance, manufacturing, healthcare, and critical infrastructure with practitioner-led execution and measurable risk reduction.
Every material finding is validated by an experienced operator. Automation supports judgment — it never replaces it.
Security posture is measured and tracked over time. Weekly monitoring, quarterly validation, and clear trend analysis.
Findings, evidence, remediation, and context persist across assessments. Your security program has history and trajectory.
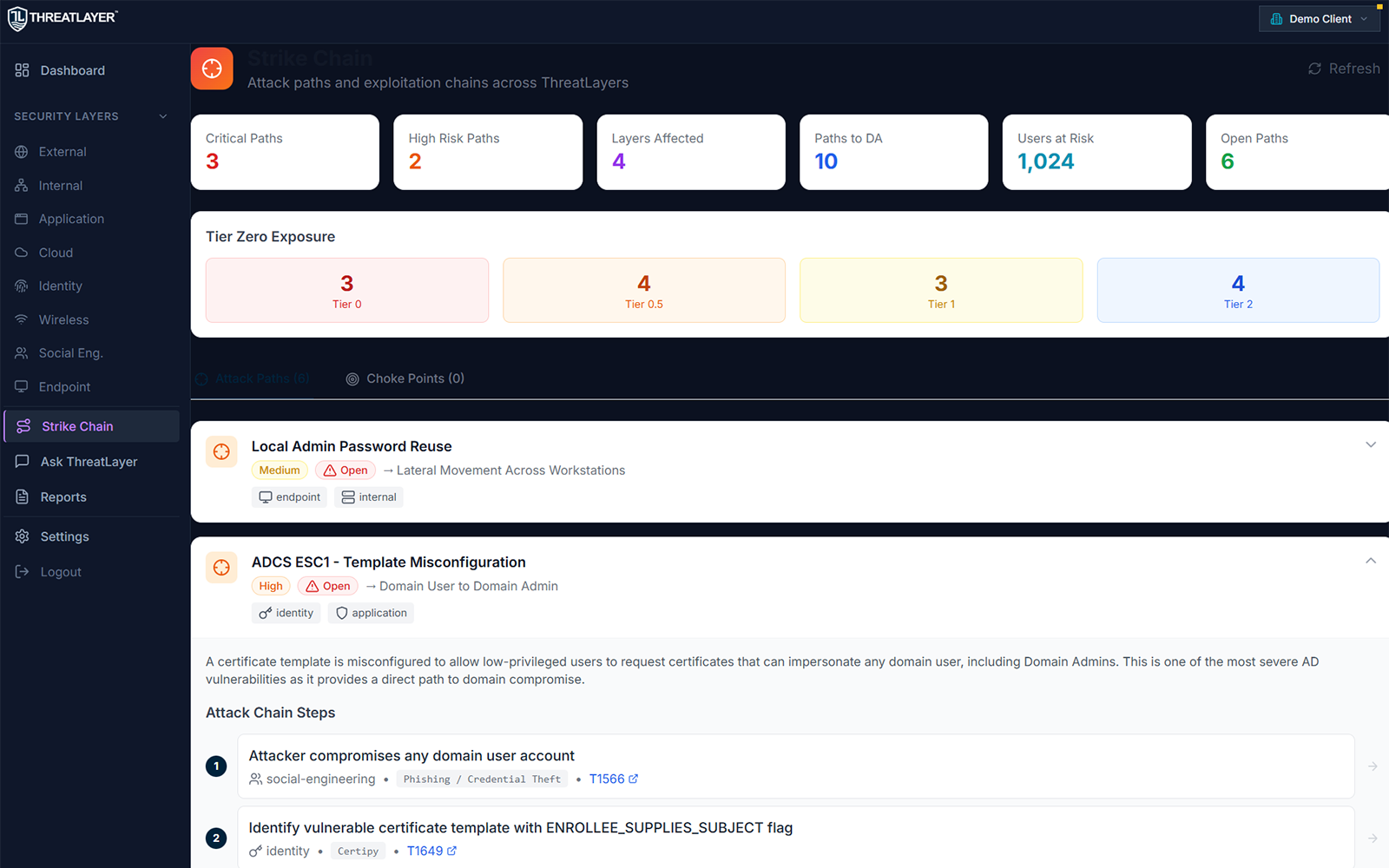
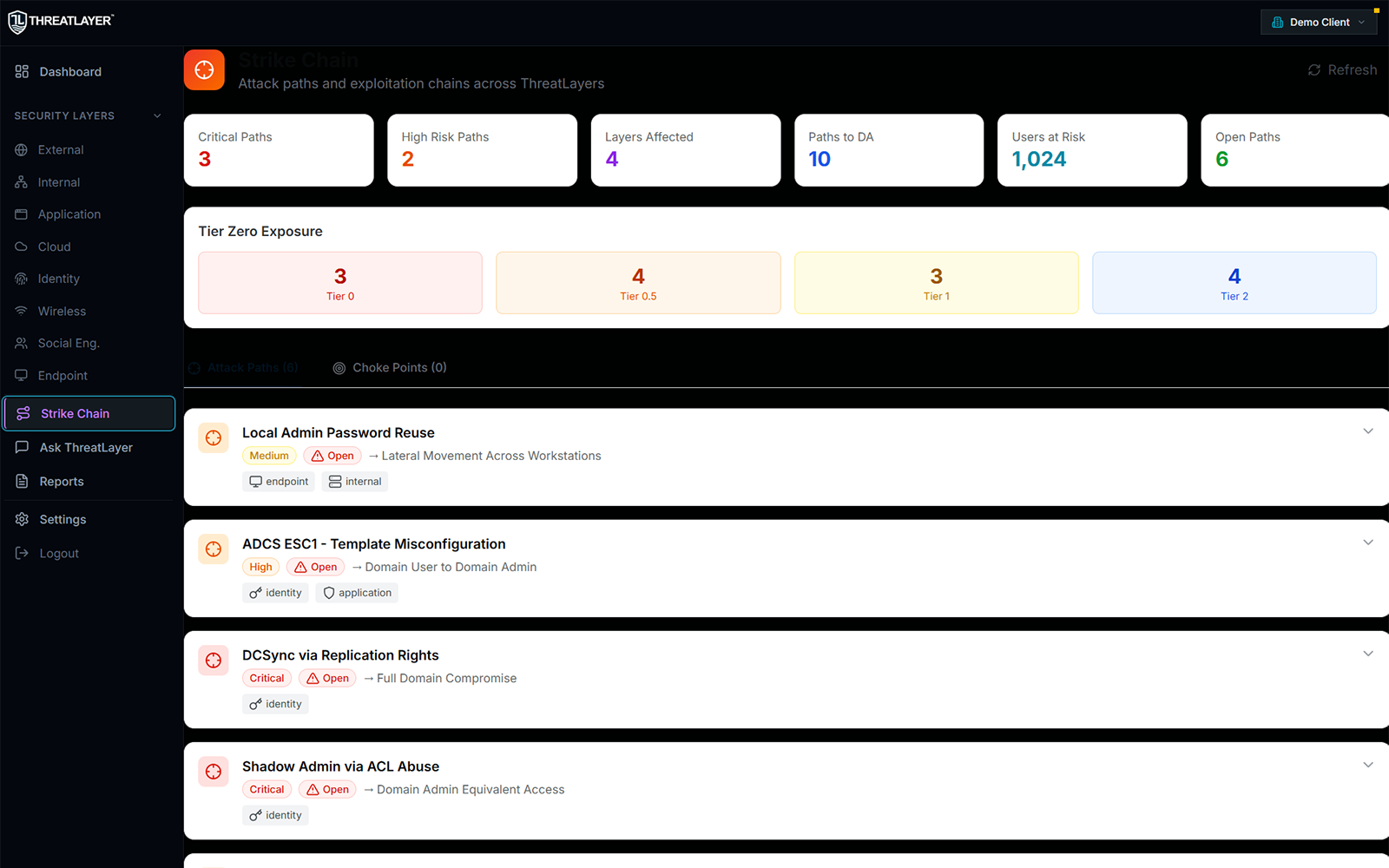
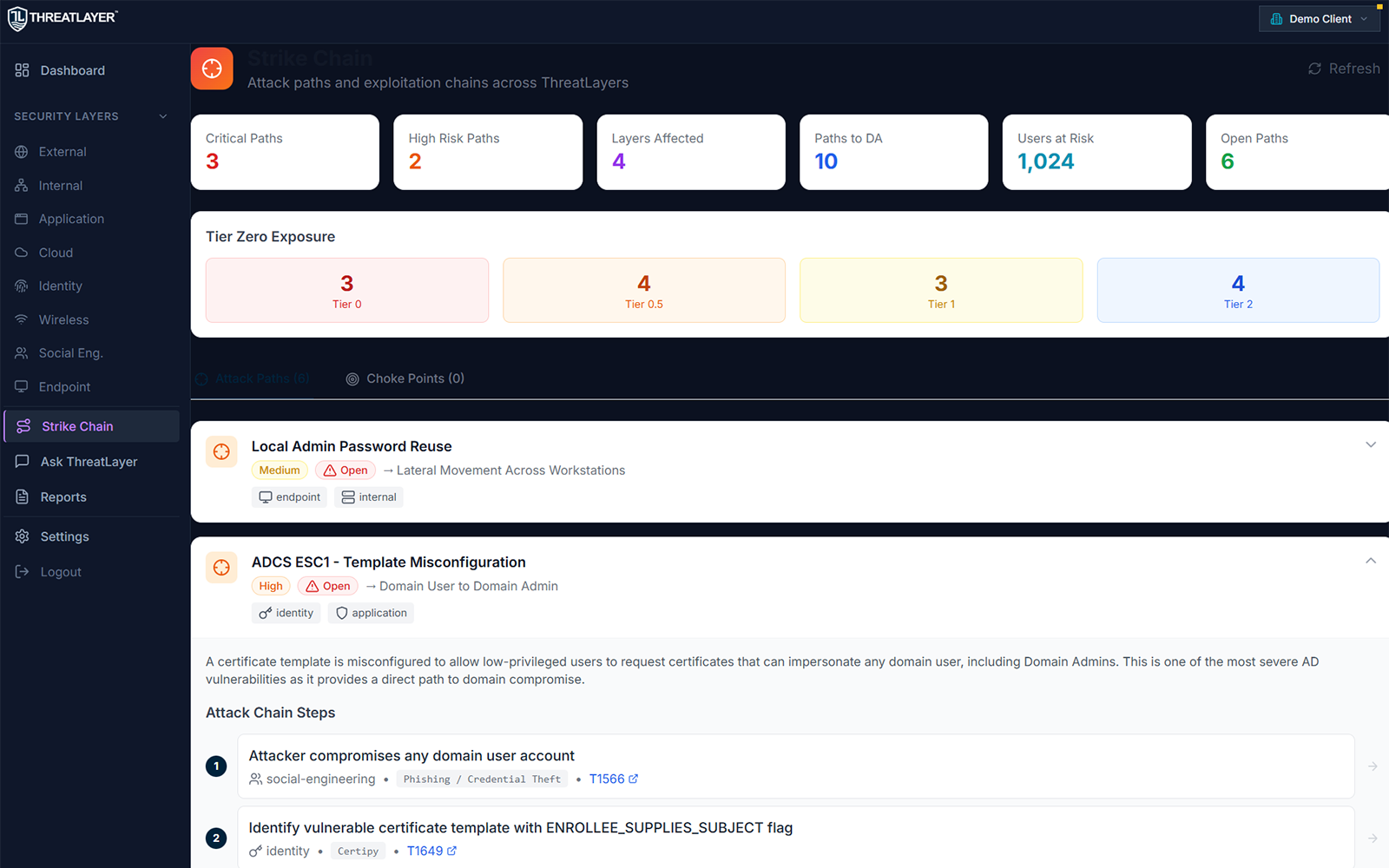
Strike Chain shows how vulnerabilities chain into real compromise paths so teams fix what actually reduces risk.
ThreatLayer is a managed cybersecurity program with expert execution, recurring validation, and accountable follow-through, supported by a unified platform.
Findings, evidence, remediation, and trends live in one place. Your security posture gains history, context, and measurable trajectory.
Strike Chain maps how vulnerabilities chain into real compromise. Fix what matters most, prove improvement over time, and report with clarity.
ThreatLayer is a complete security program designed to continuously reduce risk combining assessment intelligence, attack path analysis, and remediation lifecycle management.
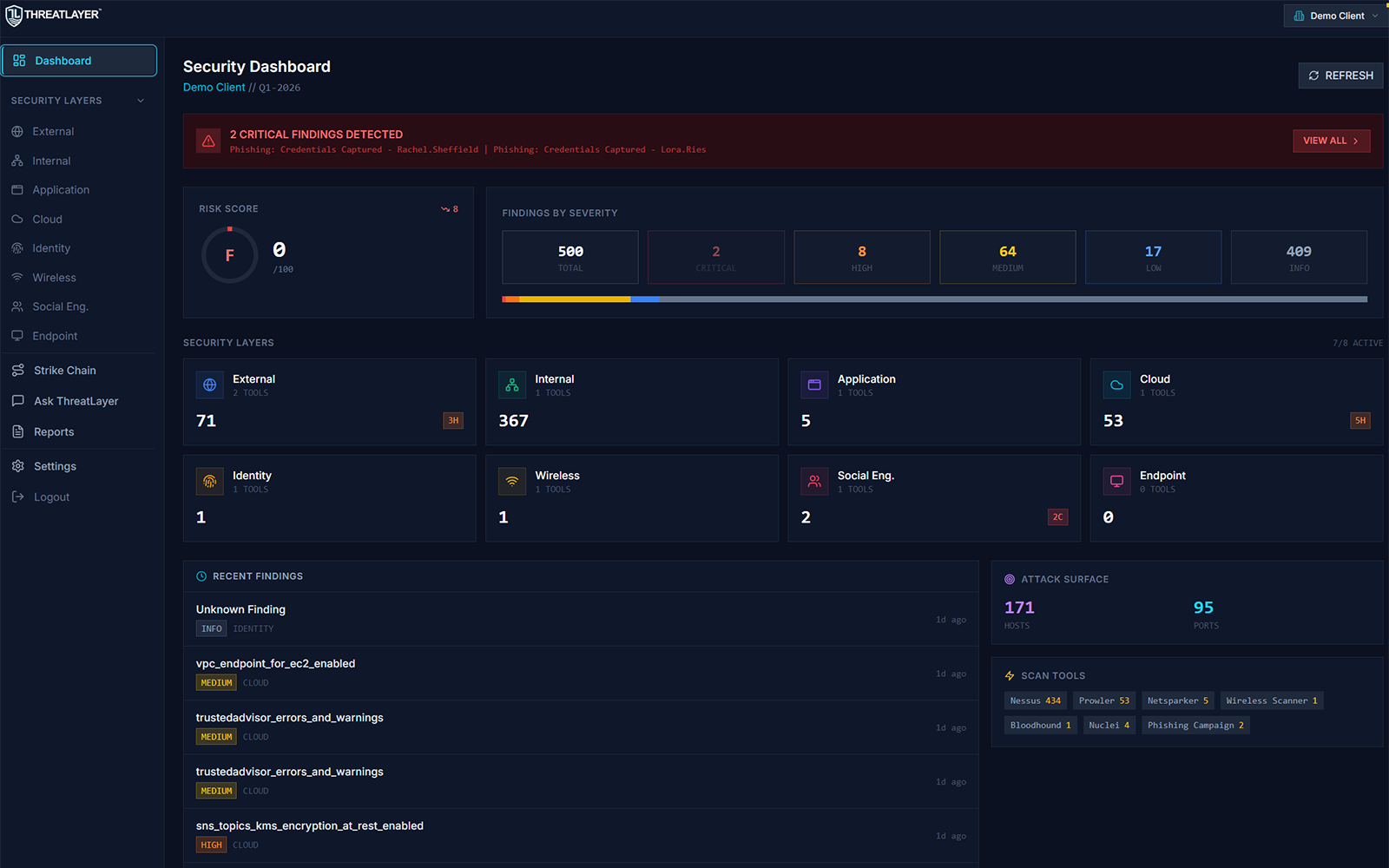
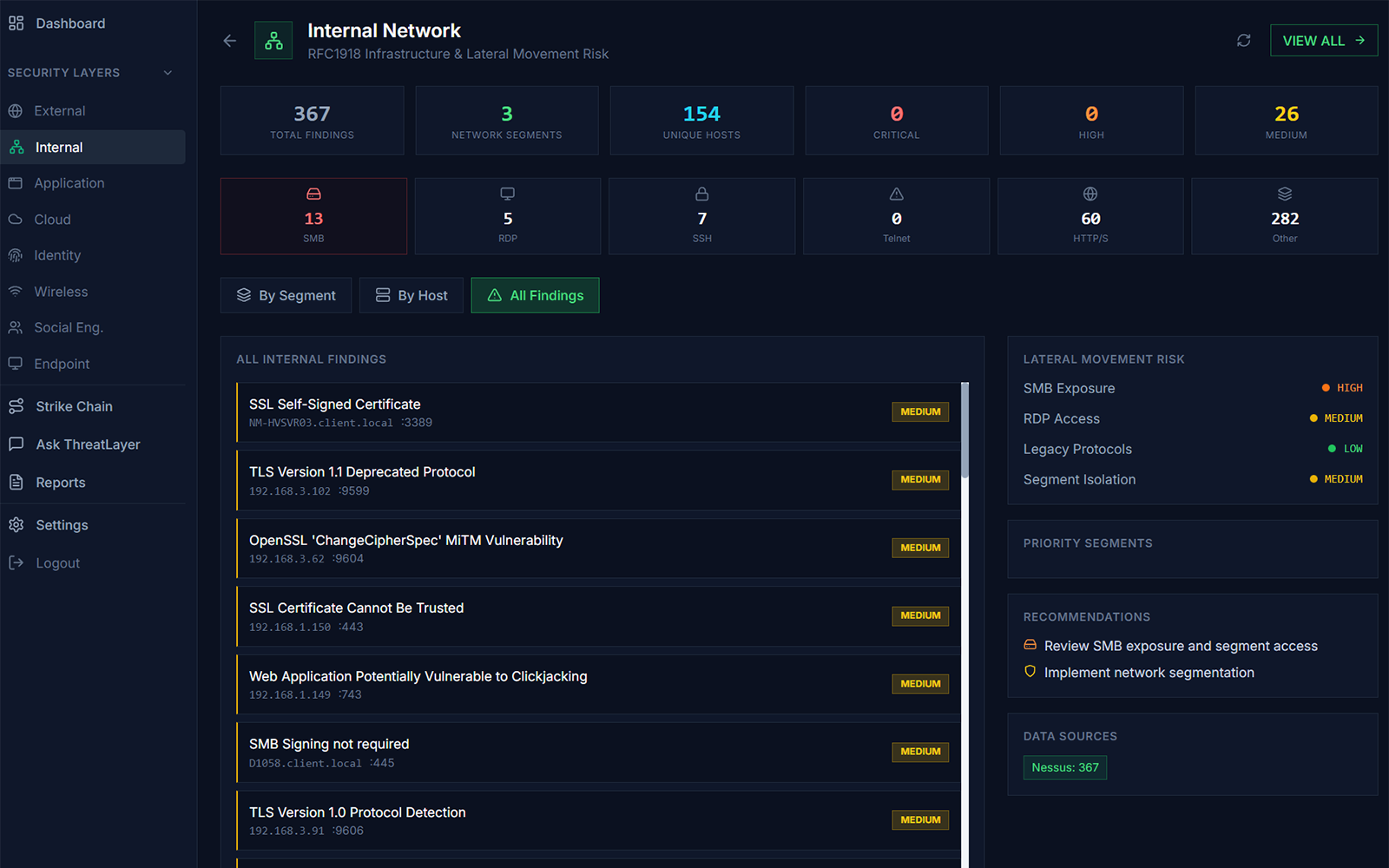
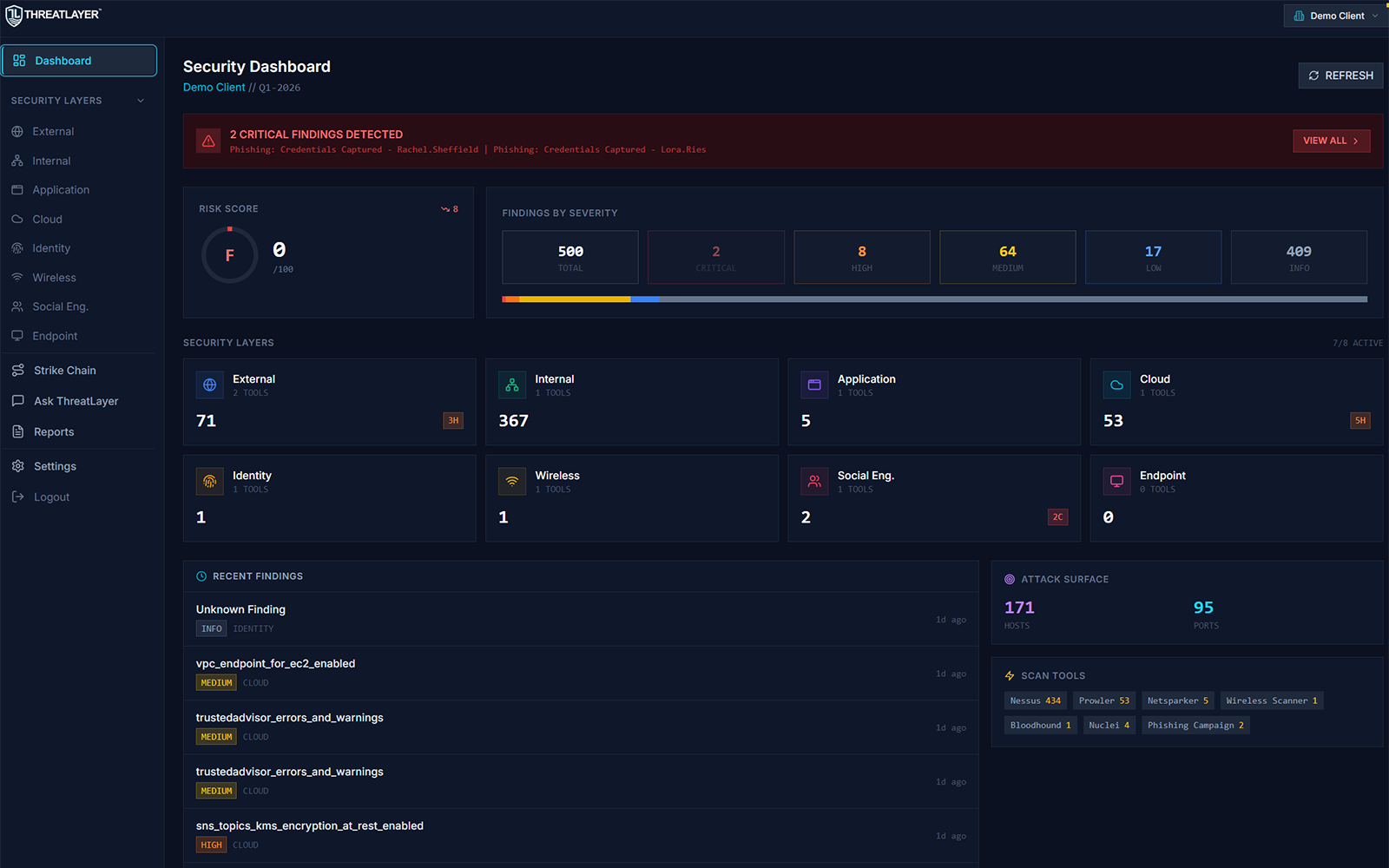
Organize findings across External, Internal, Identity, Cloud, Applications, Wireless, and Social Engineering.
Understand attack paths and chainable risk conditions across layers without exposing exploit playbooks.
Executive-ready risk translation, governance alignment, and measurable improvement over time.
ThreatLayer connects exposures into real-world risk context then drives action through prioritization and remediation tracking.
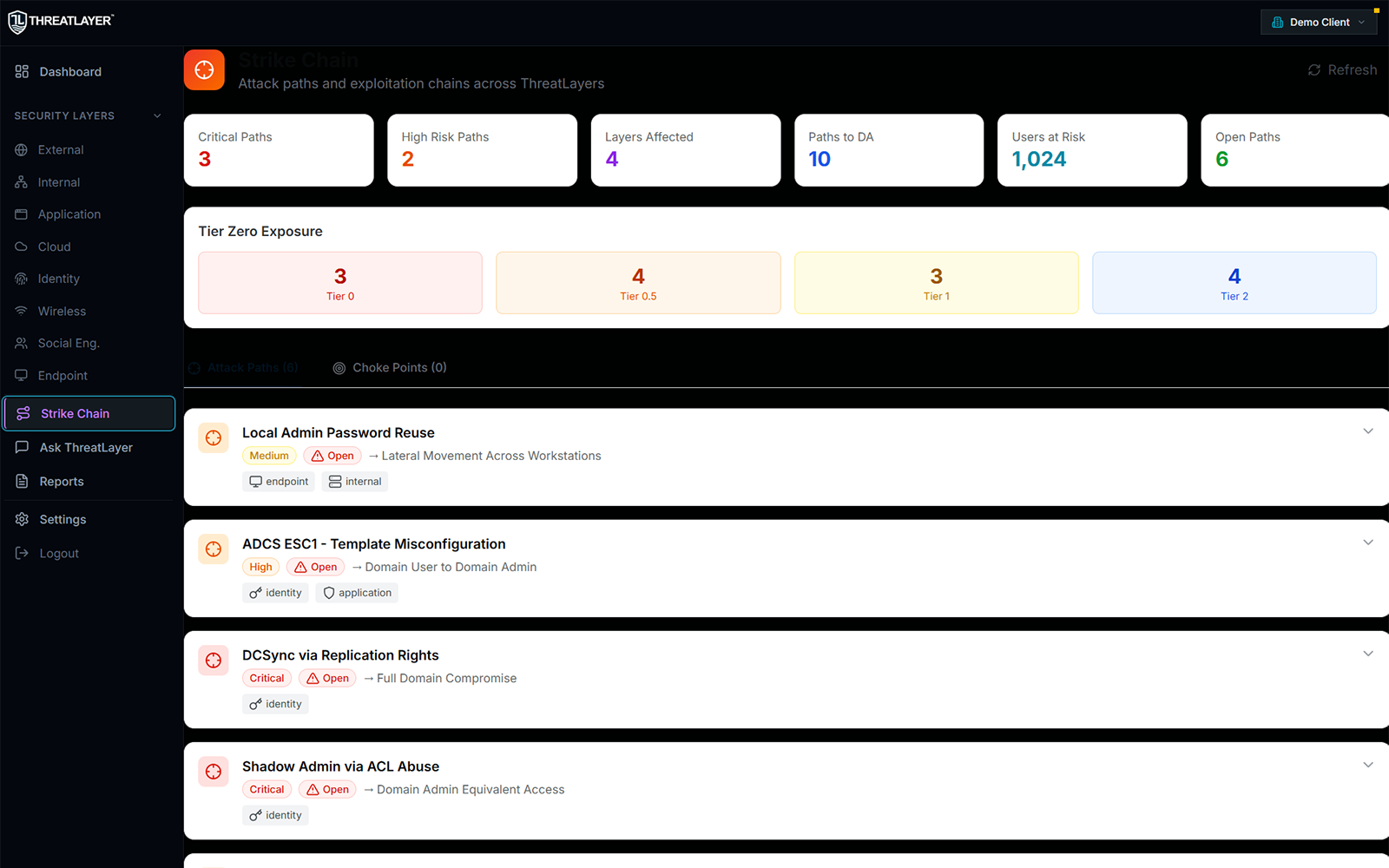
Vulnerability lists don’t show the real problem. Strike Chain maps how misconfigurations and weaknesses chain together into real compromise paths so you can break the path, not just patch noise.
*Strike Chain is live today. Blacklight and Overwatch are evolving capabilities and may appear as “coming soon” in certain views.*
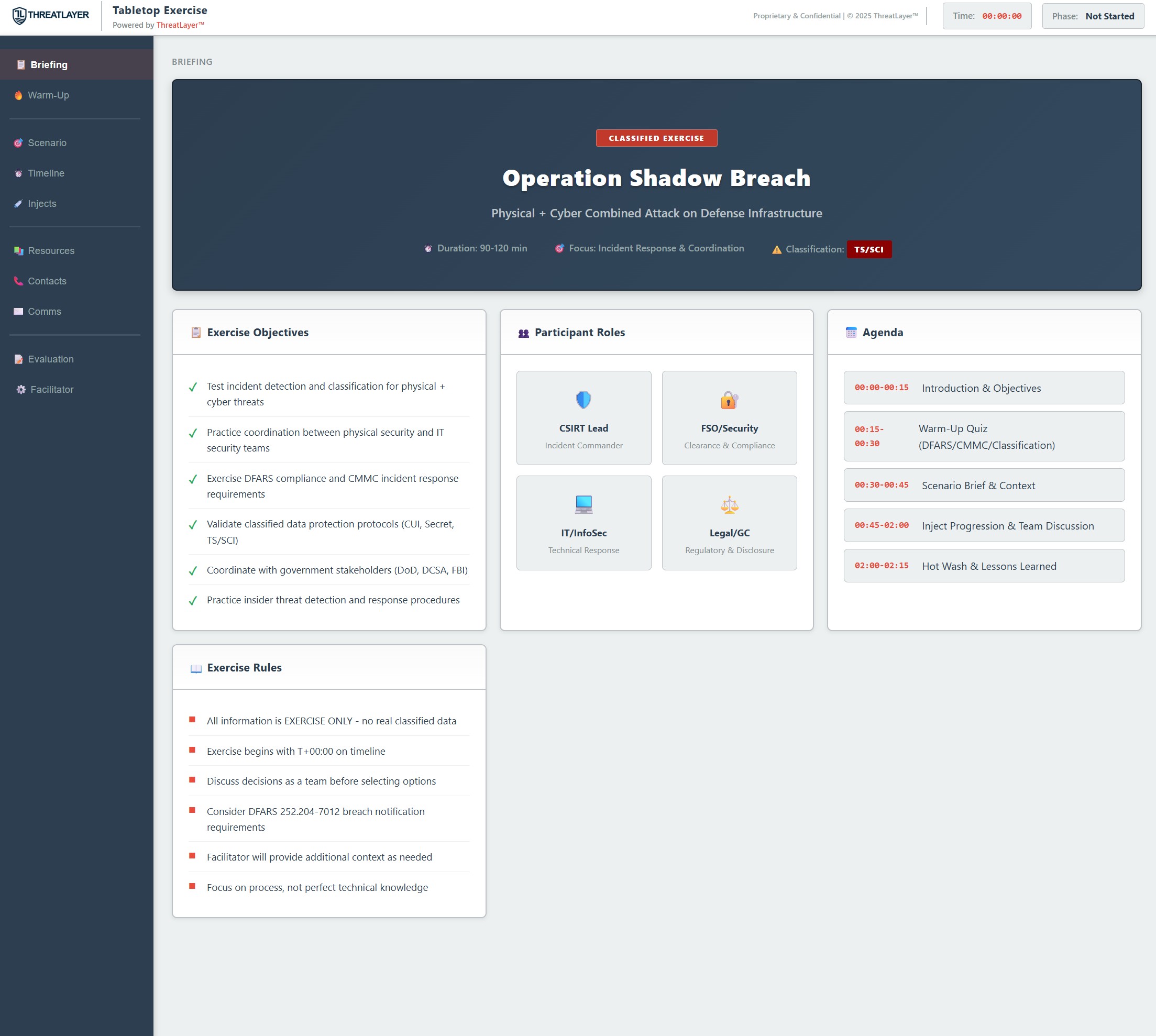
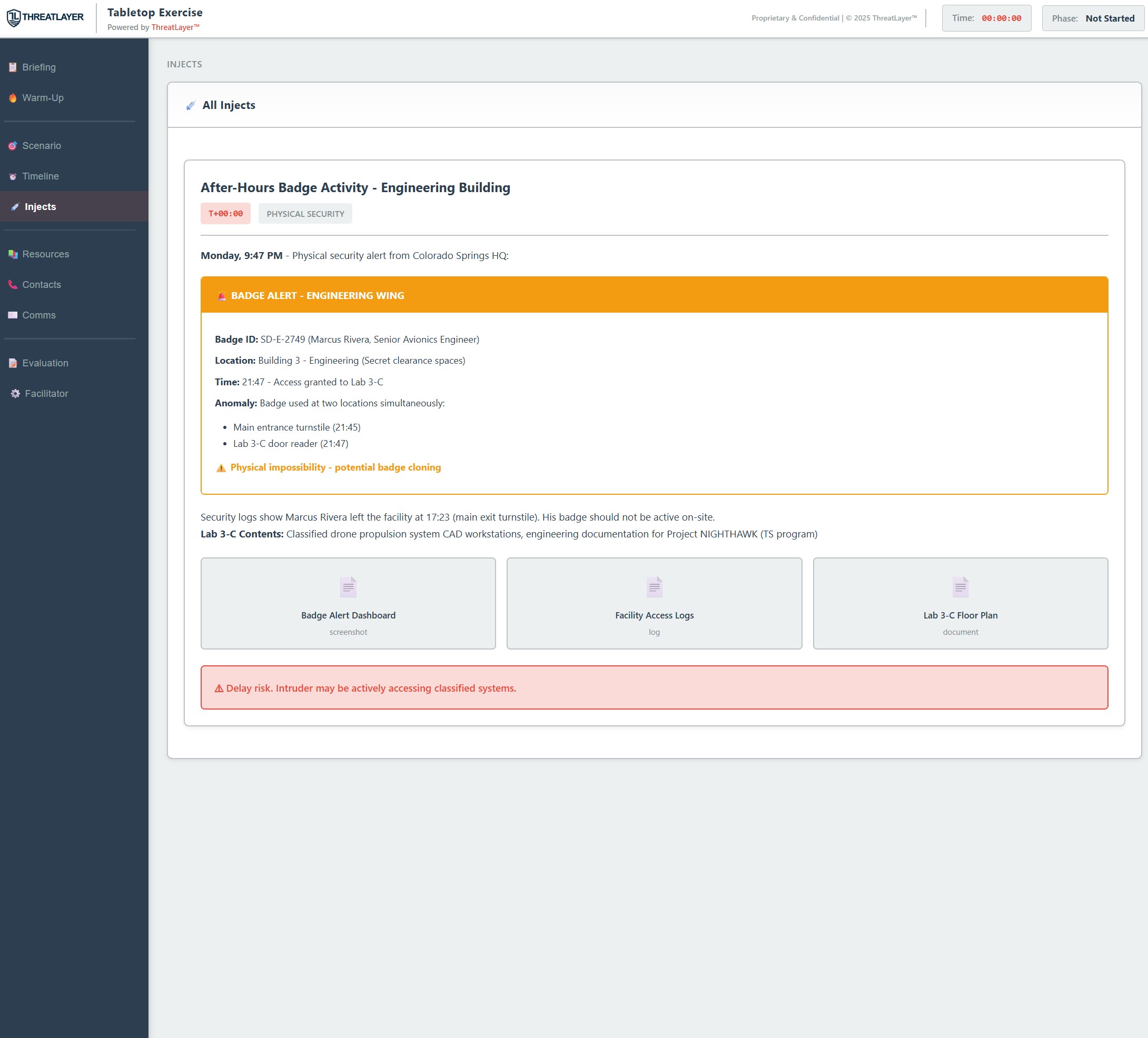
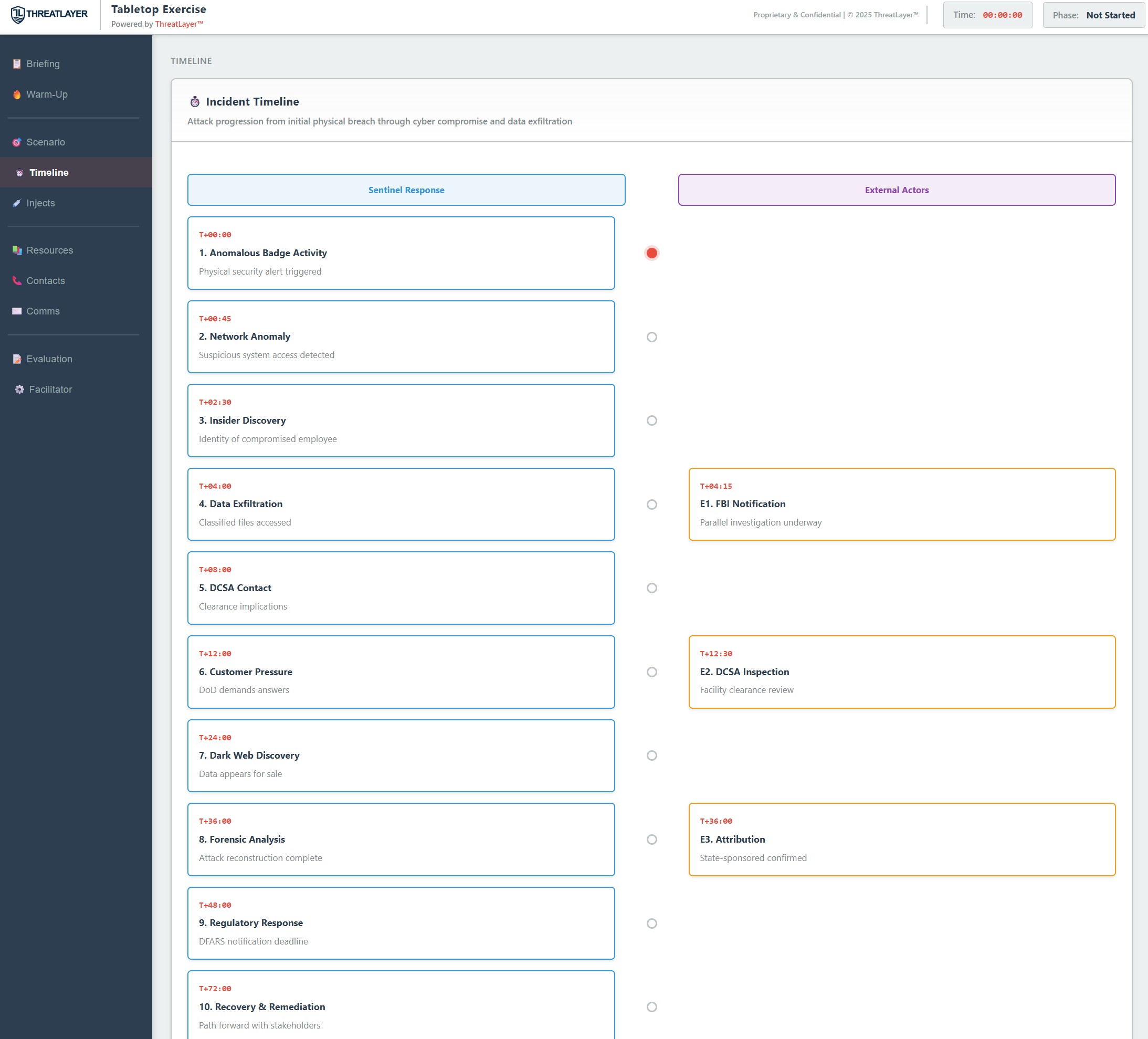
ThreatLayer Tabletop delivers a guided scenario, inject timelines, decision tracking, and evidence artifacts so leadership and responders train on a realistic playbook.

Every tier includes platform access and operator accountability. The difference is depth, cadence, and level of expert involvement designed to match your environment and risk profile.
ThreatLayer Lite is available for point-in-time reporting in the ThreatLayer format without long-term tenant access.
We operate with security-first design, strict access controls, and clear data handling standards. Security questionnaires welcome.
ThreatLayer organizes security reality into eight distinct layers ensuring comprehensive coverage without losing context or momentum.
These are composite engagement patterns based on real-world work. They are designed to illustrate typical outcomes without disclosing client identities.
Annual assessments produced long reports but remediation stalled and repeated issues returned each year. ThreatLayer established a program baseline, tracked progress, and maintained continuous visibility.
A portfolio company needed rapid risk clarity after acquisition. ThreatLayer identified high-impact pathways and informed a prioritized 100-day remediation plan.
A SaaS company needed evidence-backed answers for security reviews. ThreatLayer provided continuous assessment, reporting, and proof of improvement over time.
A fast walkthrough of how ThreatLayer combines operator-led assessment, continuous visibility, and a central system of record to drive measurable risk reduction.